DEVELOPMENT•PROJECT
AETHER
is HARDWARE based Industrial Acoustic Intelligence.

1 / 5
ALPHA_BUILD
TRADITIONAL PREDICTIVE MAINTENANCE ASKS:
"Can you send us your data?"
AETHER DEMANDS:
"Your data never leaves your building. We bring the intelligence to you."
INDUSTRIAL SOVEREIGNTY IS NOT A FEATURE. IT'S THE FOUNDATION.
PILLAR_01
Zero Latency
Decisions on the metal.
Milliseconds, not round-trips.
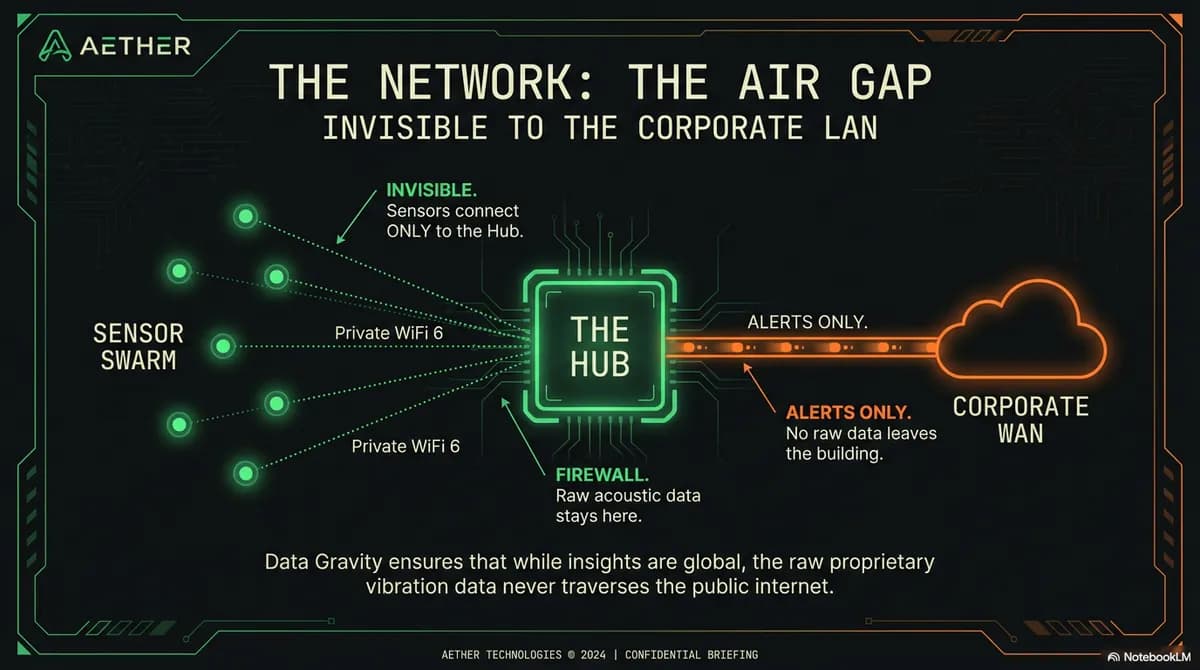
PILLAR_02
Data Gravity
100% raw data stays on-site.
Only alerts escape.
PILLAR_03
Bandwidth Discipline
Binary mathematics.
Not streaming audio.
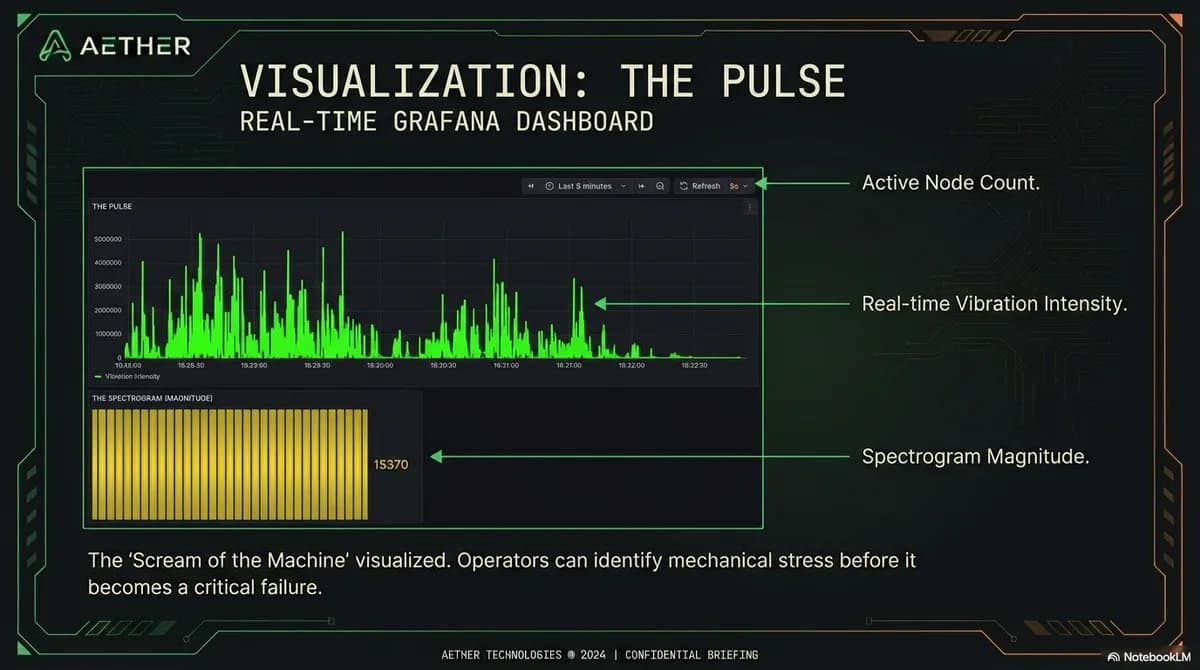
MISSION_STATEMENTDIGITIZE THE SCREAM
DIGITIZE THE SCREAM
OF THE MACHINE
Every industrial machine screams before it dies. Aether listens to these vibration signatures— the subtle acoustic fingerprints of impending failure—and transforms them into actionable intelligence. Before the breakdown. Before the line stops. Before the millions in lost production.
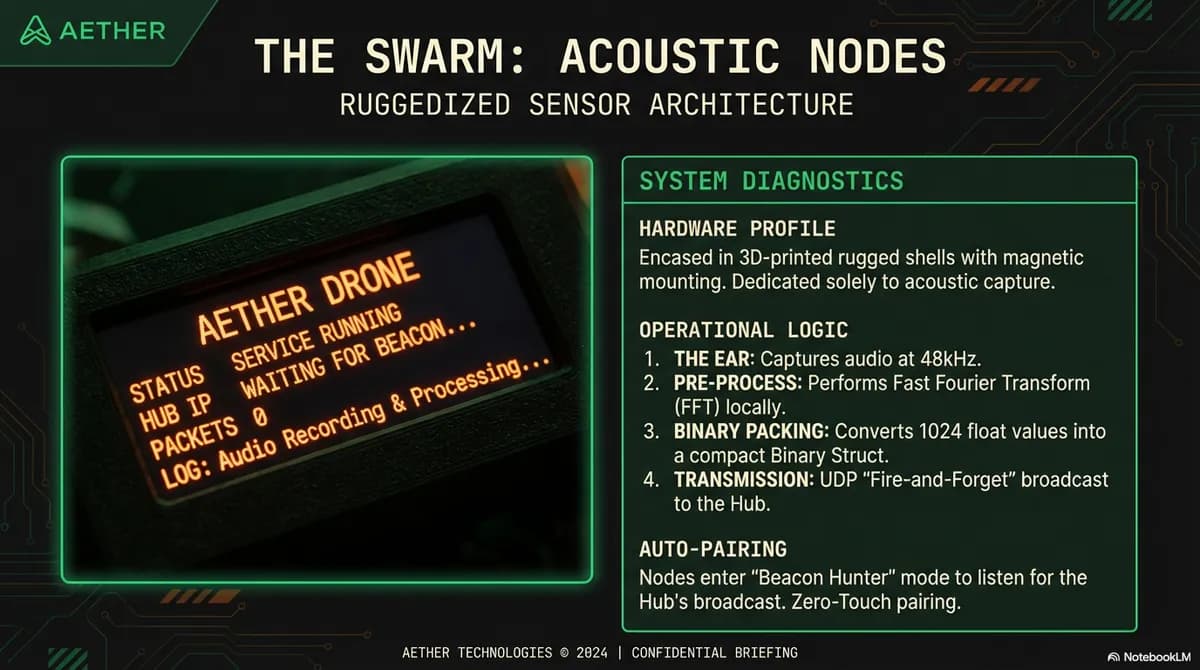
THE SWARM
The Ears
N01
N02
N03
N04
N05
HARDWARE_MANIFEST
THE AETHER KIT
A complete, turnkey fog computing platform. Pre-configured. Ruggedized. Arrives in a weatherproof industrial case. Ready for immediate deployment.
THE_CORE
The Black Box
On-premise sovereign server. Industrial-grade compute. Purpose-built for edge deployment.
QTY: 1
THE_SENSORS
The Sensor Nodes
Ruggedized acoustic sensors with on-device pre-processing. Magnetically mounted.
QTY: 10
THE_NETWORK
The Air Gap
Private mesh network. Pre-configured. Isolated from corporate infrastructure.
QTY: 1
THE_SHELL
The Case
Ruggedized weatherproof enclosure. Custom foam insert. Industrial-grade protection.
QTY: 1
STRATEGIC_PRICING
Intentionally priced below the typical CapEx committee threshold. Empowering line-of-business managers to say "yes" immediately.
$2,500
+ $500/MO SERVICE
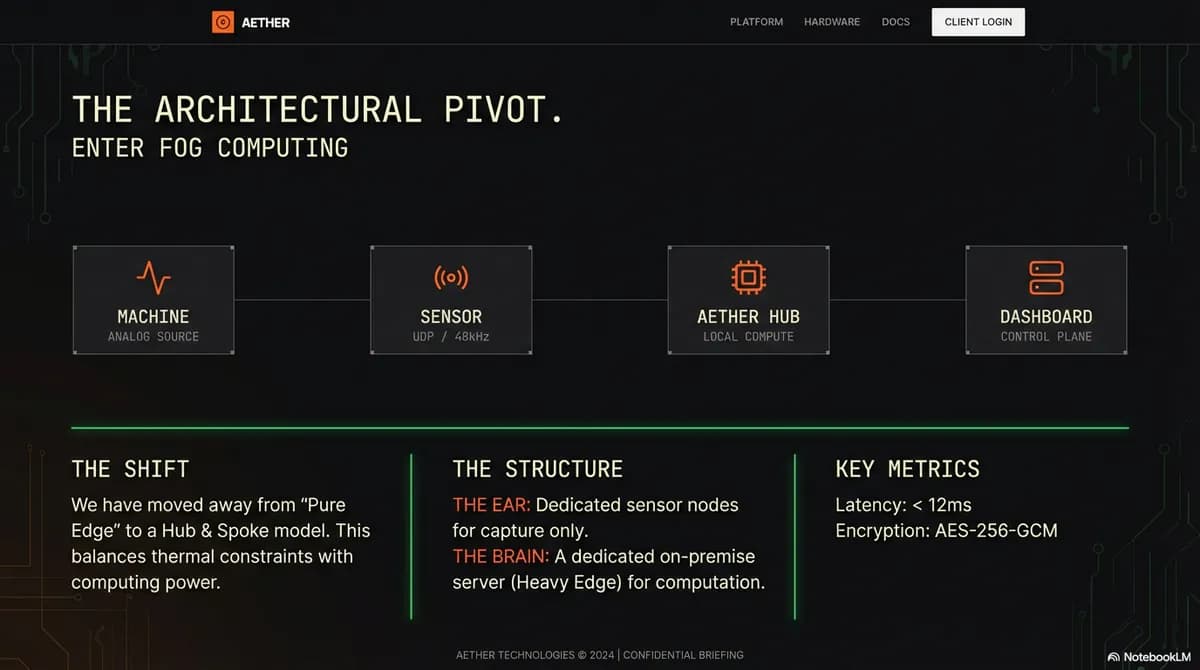
SOFTWARE_ARCHITECTURE
THE SOVEREIGN STACK
A containerized, multi-service architecture engineered for high-velocity data ingestion and real-time anomaly detection. All running headlessly on your floor.
LAYER
TECHNOLOGY
FUNCTION
STATUS
OS
Ubuntu Server
Headless operating system. Lean. Stable. Purpose-built for edge deployment.
RUNTIME
Docker Compose
Service orchestration. Isolated containers. Single-command deployment.
INGEST
Python asyncio
High-concurrency UDP server. 1,000+ packets/second without drop.
STORAGE
TimescaleDB
PostgreSQL extension for high-velocity time-series workloads. Batch inserts via asyncpg.
ANALYSIS
NumPy / SciPy
On-CPU anomaly detection. Frequency peak analysis. Threshold monitoring.
DATA_LIFECYCLE
FROM VIBRATION TO INSIGHT
01
CAPTURE
Node captures machine audio via microphone
02
TRANSFORM
FFT converts audio to frequency spectrum (1,024 floats)
03
TRANSMIT
Binary-packed UDP to Hub. Fire-and-forget.
04
ANALYZE
NumPy anomaly detection on the Hub. Milliseconds.
05
ALERT
Only actionable alerts transmitted. Data stays sovereign.
COMING SOON
JOIN THE WAITLIST
Aether is currently in alpha development. Be among the first to deploy industrial sovereignty on your factory floor. Early adopters receive priority access and founding member pricing.
BENEFIT_01
Priority Access
First in line for production units
BENEFIT_02
Founding Pricing
Locked-in early adopter rates
BENEFIT_03
Direct Input
Shape the product roadmap
PROJEKT_CONTEXT
Built by Gruppe Projekt
From concept to production-ready architecture, we engineered Aether's entire fog computing platform— hardware integration, software stack, network topology, and the strategic business model that puts industrial sovereignty within reach.
CAPABILITIES_DEPLOYED
IOT_ARCHITECTUREFOG_COMPUTINGEMBEDDED_SYSTEMSDATA_ENGINEERING
ADMIN_CONFIGURED_DETAILS
CASE STUDY
Industrial Acoustic Intelligence. Zero Cloud Dependency. Total Data Sovereignty.
TECHNOLOGIES USED
ViteTypeScriptPrismaPostgresTailwind CSS
PROJEKT DETAILS
- TYPE
- PROJECT
- STATUS
- DEVELOPMENT
- COMPLETED
- January 2026
NEED SOMETHING SIMILAR?
START A PROJEKTLet's discuss how we can build a custom solution for your business.